Control Flow Integrity (CFI)
Built for embedded performance, assuring runtime behavior
Karamba XGuard CFI:
Deterministic Validation
Of Memory Control Flow
Control Flow Integrity (CFI), is a widely understood concept, but prior to the development of Karamba XGuard, it was not successfully implemented in embedded systems.
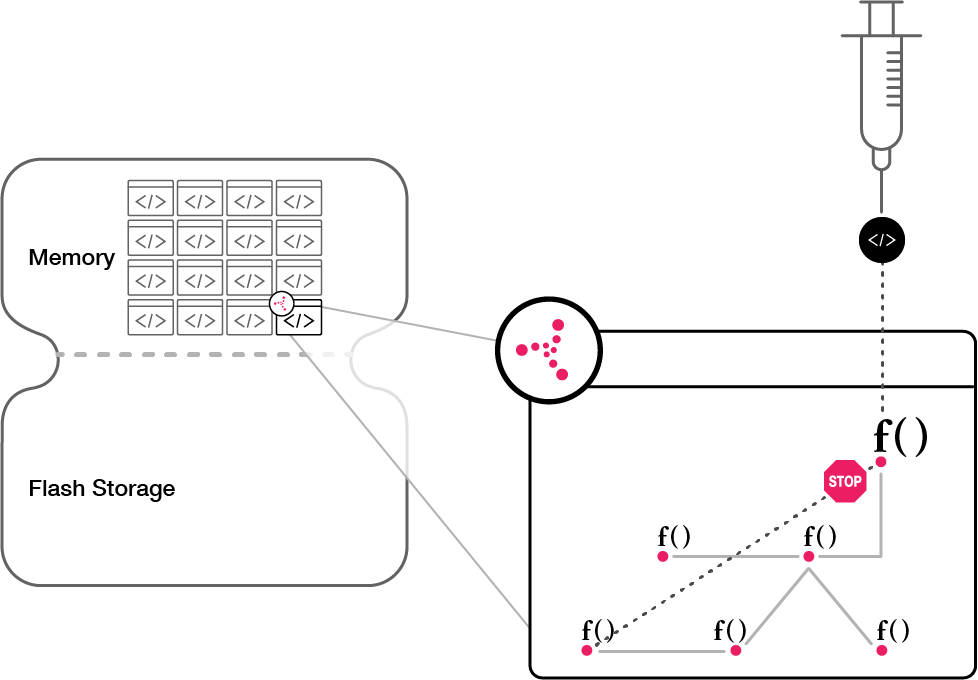
Automatically created, Karamba's patented Control Flow Graph is monitored in runtime and validates forward and backward memory address jumps. Even if the code has memory vulnerabilities like buffer overflow, XGuard will not allow exploits.
Karamba CFI is applied on the OS and application levels and protects the function calls within all binaries, libraries and scripts, as well as within OS functions.
What makes Karamba's CFI stand out from previous products that used Control Flow Integrity is its patented low performance footprint, with less than 5% CPU overhead and 10% RAM consumption.
(In the following video, Karamba Security Cybersecurity Researcher Aviv Sinai demonstrates how CFI can stop remote code execution attacks)
XGuard CFI Advantages
See Why Our Security Solutions Win Awards
Want to learn more?
Contact UsIsrael
24 HaNagar Street
Hod Hasharon
45277-13
Tel: +972 9 88 66 113
USA
41000 Woodward Ave
Building East, Suite 350
Bloomfield Hills, MI 48304
Tel: +1 833 4KARAMBA


