While it’s nice to think that all cars go to Car Heaven, in reality they go through a scrap metal recycling process. In order to recycle the remains of your vehicle, you need to get a special permit and find an Authorized Treatment Facility (ATF).
Depolluting a Car

The recycling process was designed so that the toxic materials in the car don’t harm the environment. This process requires removing any valuable parts of the vehicle that can be salvaged, remove all toxic gases and liquids. Among these are the battery, liquefied gas tank, all potentially explosive materials (including airbags and seat belt pre-tensioners), fuel, oils, fluids, filters, components containing mercury, shock absorbers, and other potentially dangerous materials.
In the depollution process, a professional mechanic accesses the On-Board Diagnostics (OBD) and with one command activates the airbags, releases the seat belt pre-tensioners, actuates-off the Anti-Lock Braking System (ABS), powers-off the engine controls, cripples the transmission and deactivates the electronic reactive devices inside the car. Then all gas, liquid and potentially dangerous materials are emptied from the vehicle. Now the car’s remains can be scraped into a metal cube.
How Unsafe and Dangerous Can the Depollution Process Be?
The depolluting process reveals a very dangerous vulnerability; imagine that with one simple command in the OBD system you can access all devices (airbags, seatbelt tensioner, etc.). Unsettling to say the least.
Having such Zero-Day command inside the OBD functions is a threat that we cannot mitigate because of the “Motor Vehicle Owners’ Right to Repair Act,” that says that every person has the right to repair their motor vehicle, not necessarily in a repair shop/garage.
We know that any hacker can attack a connected vehicle remotely without needing a tool, like through an OBD App, for example. The hacker can also exploit the OBD system, entering through the CAN bus remotely and activating the Zero-Day command while the car is driving, risking drivers and passengers alike.
Prevent a possible attack
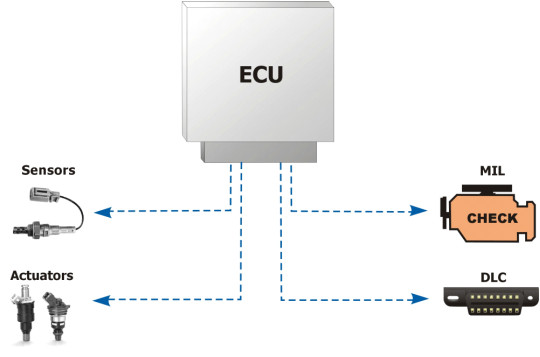
There are not many ways to prevent a possible cyber-attack while a car is driving. The only viable way to prevent an attack is by hardening the Electronic Control Units (ECUs) to factory settings. Therefore, any change on the controllers will block the command and the hacker will be unable to access the CAN bus that leads to the OBD exploitation.
When the ECUs are hardened, they don’t allow false positives or false negatives and any deviation in factory settings will result in a blocked command with negligible performance impact.
