Defending Edge and IoT Systems Against CVE-2026-31431
The Threat in Brief
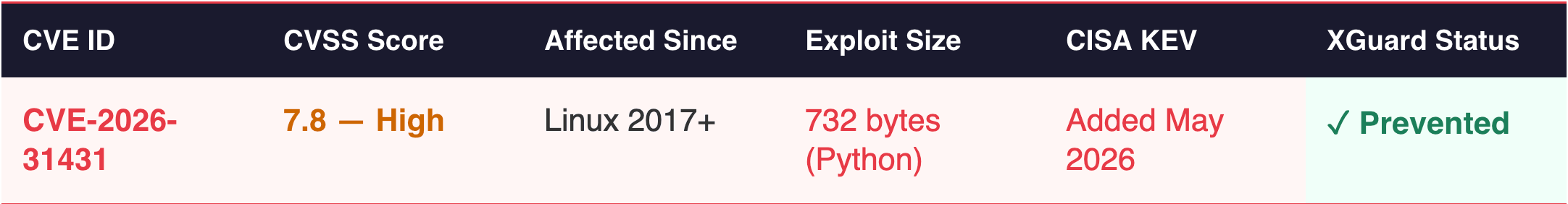
On April 29, 2026, researchers at Theori/Xint disclosed Copy Fail - a logic flaw in the Linux kernel’s cryptographic subsystem that has existed since 2017. A 732-byte Python script, using only the standard library, is all it takes to escalate from an unprivileged user to root on virtually every major Linux distribution and break out of containers entirely.
What makes Copy Fail particularly dangerous is what it doesn’t do: it never touches the disk. The attack lives entirely in kernel memory — the su binary on disk remains clean, while its cached version in RAM is silently overwritten. Traditional file integrity monitoring is blind to it. Added to CISA’s Known Exploited Vulnerabilities catalog within days of disclosure, with active exploitation already observed.
The Attack Chain Simplified
The goal is simple: gain root access on any Linux system without any privileges.
- The attacker runs a malicious Python script. The script exploits a flaw in the Linux kernel that has been present since 2017, reachable by any process on the system.
- Instead of attacking files on disk, it targets the kernel’s memory cache. No dependencies, no compilation, no root required to invoke.
- The script silently injects malicious shellcode directly into the cached pages of
su— a standard system binary that runs with root permissions by design. - When
suis executed, the system reads from the cache rather than the disk. It runs the attacker’s shellcode instead of the real program — and sincesucarries root privileges, the shellcode runs as root too.
The disk is never touched. Nothing looks wrong. Root access is granted in seconds.
It is important to highlight that the attack is enabled by deploying a 732 byte python script, using only standard libraries (os, socket, zlib).
For a detailed description of the attack, please look at: https://xint.io/blog/copy-fail-linux-distributions
How XGuard Prevents It
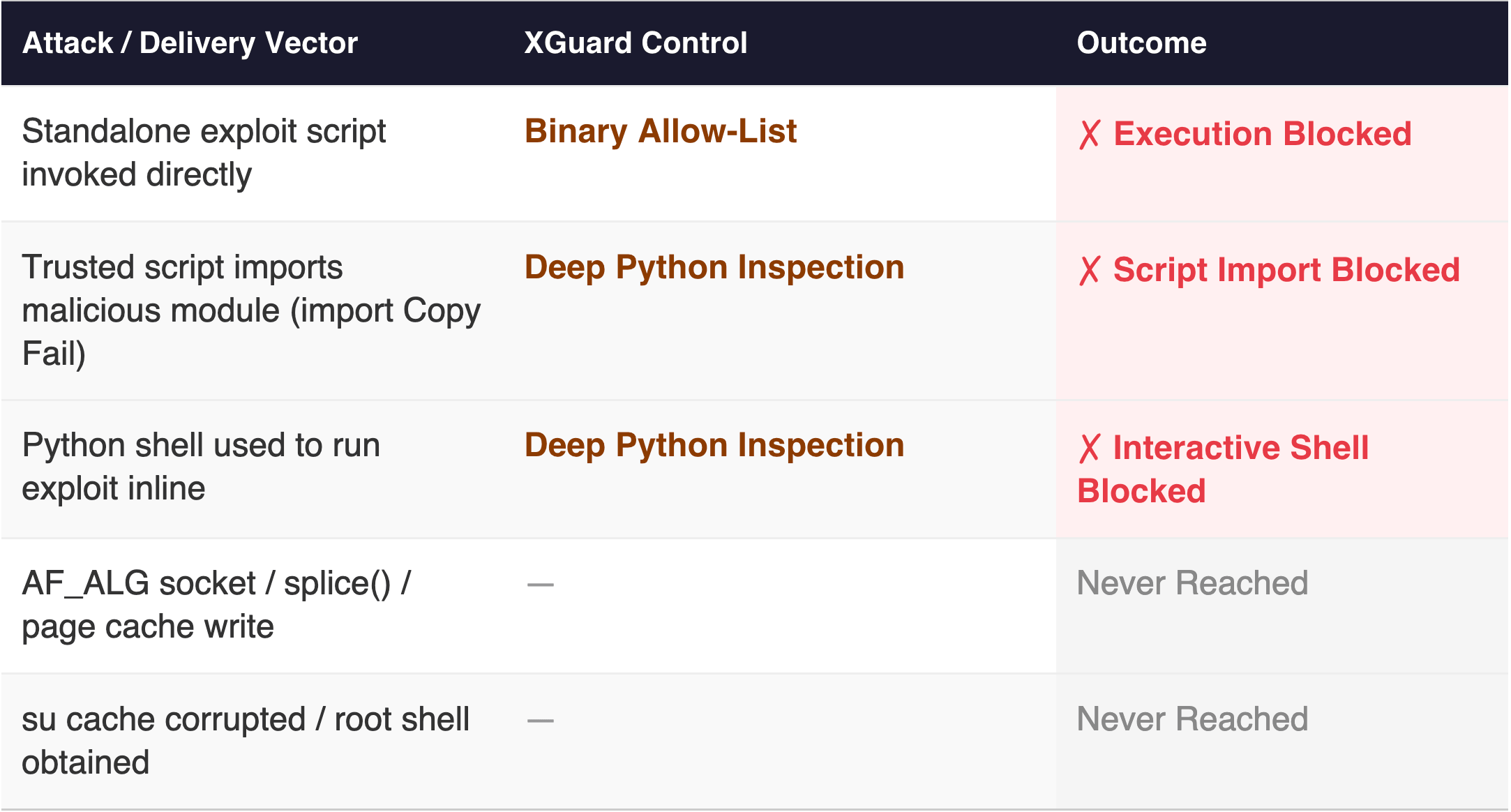
XGuard stops Copy Fail through two primary enforcement controls: the Binary Allow-List and Deep Python Inspection. Both operate before the kernel is ever touched.
Prevention 1 - Allow-List: Block the Exploit Script at Launch
XGuard enforces a cryptographically signed Binary Allow-List built from the device’s known-good software baseline at build time. Every executable, shared object, kernel object, and script on the device is accounted for. The Copy Fail exploit - a Python script that has no business existing on a production edge or IoT device - is not in that list.
When the exploit script is invoked, XGuard rejects its execution immediately, preventing the exploit from starting. The su cache pages are never touched. The attack chain terminates at step one.
This protection is exploit-agnostic. XGuard does not need to know about CVE-2026-31431, have a signature for it, or wait for a patch. Any script not in the approved baseline is rejected - covering zero-days and N-days alike, before they can interact with the kernel.
Prevention 2 - Deep Python Inspection: Block Python-Based Bypass Attempts
A sophisticated attacker aware of XGuard’s Allow-List will attempt to deliver the Copy Fail payload through a Python process that is already trusted. XGuard’s Deep Python Inspection validates not just the top-level script, but every module import, dynamically loaded file against the Python Allow-List policy, and also limits interactive use of Python. Two bypass scenarios - and how XGuard stops each - are described below.
Scenario A - Malicious Module Import
An attacker leverages a pre-existing import mechanism in a legitimate, Allow-Listed Python application. The parent script is trusted. A tampered imported module that is called in runtime carries the full 732-byte exploit payload and is not in the Python Allow-List.
XGuard’s Deep Python Inspection intercepts the import at resolution time. The module is evaluated against the Allow-List before any of its code executes. Because the Copy Fail payload is not in the pre-approved, allow-listed scripts, the import is blocked and execution halts.
Scenario B - Python Interactive Shell
An attacker with access to a Python-enabled application - or one that exposes an interactive Python terminal - may attempt to use it as a launchpad: typing the exploit script directly into the interpreter to execute the attack.
As IoT and Edge devices are not supposed to run interactive Python as part of their modus operandi, XGuard Deep Python Inspection blocks interactive Python activities, and prevents the Copy Fail from being applied interactively.
Defense Coverage Map
The Takeaway
Privilege escalation starts with local execution by a low-privilege process. Blocking the user from running unallowed files or scripts blocks the privilege escalation attack at its root.
As risky as Copy Fail is, due to its minimal footprint and ability to bypass traditional security mechanisms, XGuard Allow-List and Deep Python Inspection address the problem at its root: the exploit and Python-based delivery variants require running code that isn’t part of the device pre-approved executables or scripts. XGuard doesn’t need to recognize the attack — it simply doesn’t permit anything that wasn’t trusted by a signed XGuard policy.
For edge and IoT deployments where emergency patching is operationally costly or infeasible, this is the strategic case for deterministic hardening: break the kill chain before the kernel is ever involved, regardless of CVE age, and sustain that protection against repeated, automated exploit attempts at machine speed.
Sources: Theori/Xint, copy.fail, April 29, 2026 — Karamba Security, XGuard Feature Overview, March 2026